Cybersecurity protocols and management built for high demand it environments
List cybersecurity protocols and management built for high demand it environments
-

Qr code link to this post high quality, natural and powdered turmeric for salehygienically processed, dehydrated, sterlised, packed and sealed in polythene bags
₹ 400
-

Qr code link to this post high quality, organic and powdered turmeric for salehygienically processed, dehydrated, sterlised, packed and sealed in polythene bags
₹ 400
-

Cubot offical shop for high quality & affordable smartphones and rugged smartphoneprofessional customer servicessecure payment systemcom/g/zk14cxa3ibeb4fa7dfca45d921/no minimum order quantitypotential to partner with usone year warranty copy/paste: https://adfriendly helpful customer serviceseu after-sales outletsimple and trust, cubot aims to be a credit worthy high-tech corporation in the worldwhy choose cubotfree or low cost shippingtt has strong power to research by itself and to run the brand cubot in the global market, integrating r&d, production, sales, warehouse and logisticsyou can buy the best quality mobile phone with the lowest price
-

If you are looking for high end jewellery in delhi, then kanjimull jewellers is an ideal choice for youtheir collection is authentic and thoughtfully crafted by skilled artisans in indiathey have a variety of designs that will add elegance to your look
http://wwwkanjimulljewellerscom/
d-30, defence colony, first floor, new delhi-110049
01141403500Delhi (Delhi)
-

Stylish and comfortable 3 seater high quality sofa for your home at low price
₹ 5999
-

Very beautiful looking watches only for high standard peaple
₹ 149
-

For high blood pressure, gathia, migraine, gud grasping power etc
₹ 999
-

For high quality photo & vidios shootthe best award winner
₹ 47500
-

For high quality shoe order nike adidas different prices
₹ 1400
-

Online video editing system for high profile users:- dell branded machine:- core i7 processor delll branded motherboard 4gb ram 500gb hdd 15gb intel hd graphics cabinet & smps cost:- /- bulk available
₹ 21000
-

Very high qualitywalker foldable and with musicthe huggie in the picture is free of costcall me at 948o273o9o
₹ 500
-

School big bag for high standard childrenproduct name (fashion time)
₹ 589
-

Office table and boss chair for sale only for table in excellent condition metal body and big storage with locking system 4& half feet long 2& 1/2 feet wide very strong and attractive today may be the last day to buy it from vejalpur address then onwards it will move to gota ahmedabad
₹ 3599
-

Bought it from ahmedabad for 20 k it's only worn onceit is in very new condition, anyone who is interested can ping me thanks
₹ 15000
-

It's used for one time and the size for me didn't fit so iam selling it for very cheap
₹ 700
-

I bought it for my marriage, it is by manyavar and size is 36
₹ 20000
-

It is also helpful for preparing for iit and other examsthe book is in excellent conditiona very good book for physical chemistry
₹ 110
-
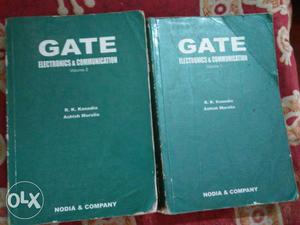
It helps me a lot in my gate examit is very useful for gate aspirantit is in very good condition
₹ 550
-

Bought it for rs selling it for less price as it needs some service if it is shaken it is working fine if intrested contact me
₹ 400
-

Gray and black polka dot and floral long sleeve high neck dress
₹ 2800
-

I bought it and used only for 2 monthsnow i want to sell itit is in good condition
₹ 8000
-

It's an imported product withso if anyone interested then inbox meit is totally soundless pumpit's a oxygen pump for fish aquarium
₹ 200
-

There is air pressure in this shoes which the leg to be stableit is really very helpful for people who have fractured leg it can be wear in any leg, right or left doesn't matterankle shoes for fractured person
₹ 3800
-

Used sleeng bag, bought it for /-,selling it for 500/- as it is used, genuine buyers only reply plsss
₹ 500
-
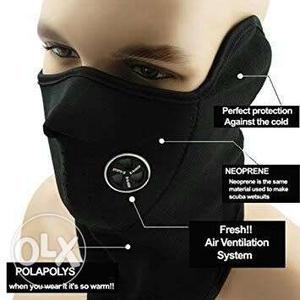
When you wear it it's so warmbest quality facemask for winter seasons it covers face nose and ears made with imported material
₹ 120
-

Philips sterilizer for feeding bottles it's just 2 months oldits price is for new my baby has been grown up that's why i am selling itgenuine customer plz
₹ 2500
-

Now it's available in low cost buy it and try oncewater resistant bagpackwith dark black bag with highest black body radiationthis bag is actually ment for laptop but it can use as college bag
₹ 800
-

Soaf and 2 cot and dining table all high quality wood
₹ 10000


